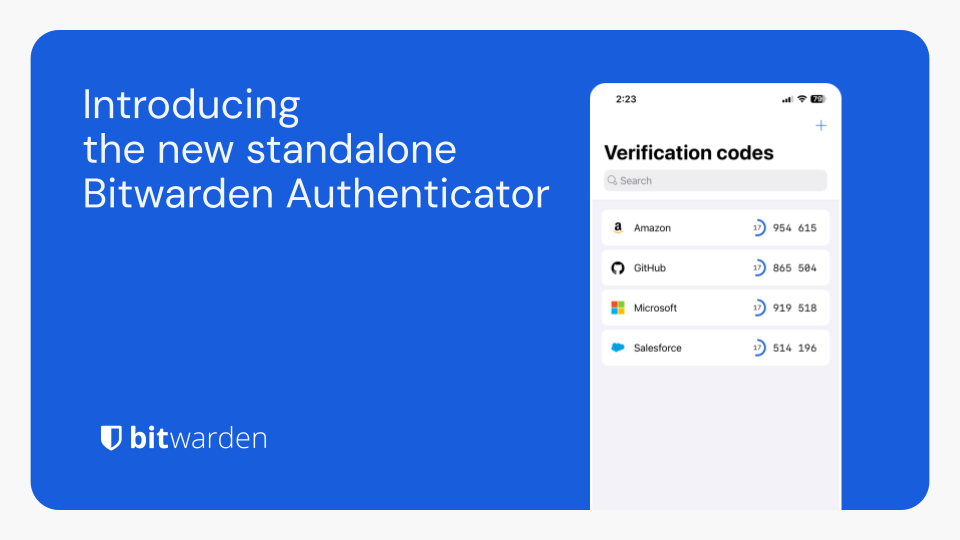
Bitwarden Authenticator is a standalone app that is available for everyone, even non-Bitwarden customers.
In its current release, Bitwarden Authenticator generates time-based one-time passwords (TOTP) for users who want to add an extra layer of 2FA security to their logins.
There is a comprehensive roadmap planned with additional functionality.
Available for iOS and Android
This is actually really good of them to realize that there is a market for another, separate, 2FA app to be honest. I don’t trust or like Google nor Microsoft. Authy is crap and going down the drain.
Using 2FAS now but not really feeling it.
If I could self host this and have redundancy/offsite backups I would probably move to this separate solution (Outside of regular Bitwarden).
Keeping the passwords and 2fa tokens in the same app is like writing the password on a post-it underneath the keyboard.
Aegis is my absolute favorite for 2FA’s, give it a try for sure. Pretty sure it’s only available on Android unfortunately though.
Privacy friendly Ente has an E2EE cloud backed up authenticator app called Auth. In case you didn’t want to host your own, or need multi-device sync.
Or you can just self host Bitwarden and use the built in 2FA that can be attached to any login
I moved to Raivo on iOS
Same
Are you in my head? Is this an alternate account that my subconscious self uses? What is real?
Re Authy: Still use it for the backup and restore. I had a phone die in me and without that feature, i would have been locked out of so many accounts. Happy to switch if something better comes along, but backup is a must for me (and not via Google…)
This new Bitwarden 2FA does backup and restore! It was also important to me, as I had a phone stolen one time and without my backed up “emergency codes”, I’d been SOL! :)
I’m feeling you! That’s the same reason I’m looking for a alternative.
I had a phone die in me
The phone being inside you is probably why it died 😂
But on a serious note, I haven’t switched to passkeys because I don’t have a clear mental model of how to recover from losing both my phone and computer at the same time.
Well that’s interesting 😎
I never like the idea of TOTP in your password database.
It’s extremely convenient and not particularly safe. I love it, my FBI agent loves it, and my Russian hacker friend loves it too.
To be fair, a lot of sites that I consider “low security” are starting to mandate 2fa. Password manager is perfect place for these, I have more going on in my life than copying numbers from device 1 to device 2 to get my garbage picked up.
Yeah,when I got more than 30 totp accounts, I gave up on keeping them separate. Its still better than 1FA.
Why do you think its not safe? If you trust bitwarden to protect your passwords what exactly do you think is going to happen?
Even if bitwarden is compromised in someway in the future, all that data is still encrypted and would still be highly unlikely to actually be accessed in any usable form.
The only risk is if you use a bad master password. Which is the biggest risk of using a password manager regardless.
I think a bigger concern is if someone managed to access bitwarden on a logged in instance. Think, leaving your laptop open, or someone steals it from you. If theres two apps for logging then both apps need to be accessible/compromised.
This seems more like a user issue then a security issue. If you are avoiding this feature because you have to idiot proof your security against yourself, your probably going to be compromised at some point anyway.
As for your example, this seems easily avoidable by
- just have the vault timeout be set low (1 minute) and to logout.
- Not leaving your password manager unlocked and unattended (wtf are you thinking lol)
If you are going to write “user issue” in the future, maybe stop and think. You might be calling someone dumb and be defending bad design at the same time.
I think if people read that comment and think they are being called dumb, that’s completely on them and probably a good time to look themselves in the mirror.
Nothing wrong with the design. Its literally just making thing easier at no cost to the user.
deleted by creator
The point of 2FA/MFA is that you need two separate things in order to gain access. By having them both be the same then suddenly the attacker only needs to get one factor. Sure, it’s probably low risk, but it’s still risk.
Basically then it degrades to a very strong password that can’t easily be phished.
Which is still pretty good in my book, but not as good as a second device.
Not really. You still should be using MFA to access the vault itself before you can even get to the Token.
Yeah, of course. A very strong password that can’t easily be fished that is stored in Bitwarden. I thought that was implied.
“Basically then it degrades to a very strong password that can’t easily be phished.”
I’m disagreeing with this, in that you are still (hopefully) using 2FA with your vault. Therefore whatever your accessing in that vault whether its a TOTP token or a password is still protected by MFA and not just a “very strong password”.
Putting a TOTP token inside a vault protected by a strong password and another form of authentication is no less secure then having it be separate from the vault.
Considering a password manager that also stores your second factor to be 2FA, assuming that it requires two factors to authenticate with on its own, is basically the same thing as considering logging into a site via SSO that itself requires two factors to be 2FA.
It’s also the same as considering a hardware security key with a PIN-protected Passkey to be 2FA.
Yes but you would still have 2FA.
You would still be using 2fa to access your vault. So in effect anything in that vault has more then 2 factors of authentication as it requires MFA just to get to the password.
Yes but you would still have 2FA.
You would still be using 2fa to access your vault. So in effect anything in that vault has more then 2 factors of authentication as it requires MFA just to get to the password.
Seems a bit odd to roll this out without having the ability to import from other authenticators (at least on android). Feels like a pretty basic feature.
Its on their roadmap and it says import should be coming this month so it’s not too long of a wait.
Cool idea for anyone who doesn’t already use Bitwarden for their passwords, but I would be awfully sceptical of having my passwords and 2FA codes stored on the same service - only one breach required to royally screw me up
2FA is entirely offline. So it’s not really the same service and there’s nothing to breach.
True. While it’s definitely more secure than their other 2FA offering (storing them with your passwords), it’s still the same developers making both - so it still feels like putting all my eggs in one basket.
For IOS I can see this as a valid option, because unless you are willing to trust Microsoft, Google, or Authy with your 2FA, which I personally don’t think one should, then you haven’t got too many options.
But on Android there are plenty others that are known to be reliable, Aegis for example, so the value proposition is lessened for me at least.
While I’m still waiting for mobile passkey support 😢
Ammmm 2fa is a Bitwarden premium feature long time ago. It works pretty well in combination with password manager
Use vaultwarden