cross-posted to: https://sh.itjust.works/post/12856684
I have the following topology:
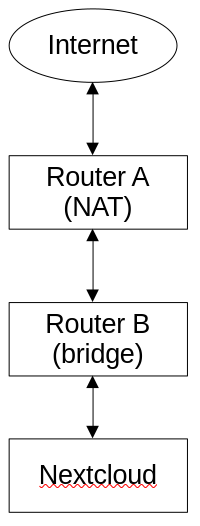
The device running Nextcloud (snap) used to be connected to Router A, but I have recently added a bridge (Router B) and I moved Nextcloud’s device to that bridged network; however, as soon as Nextcloud was moved to Router B, the portforward on Router A seemed to stop working – as in I cannot connect to nexcloud from the public IP anymore. Bridges operate at layer 2, so this should make no difference whatsoever (this is reflected in the fact that other services (like SSH) still work perfectly fine portforwarded – it’s only Nextcloud that doesn’t work), which leads me to think that it is a Layer 7 (i.e. Nextcloud) issue. What’s going on here? How can Nextcloud even tell that it’s been placed on a bridged network?
EDIT (2024-01-16T00:19Z):
I performed a network capture on the device running Nextcloud, and it appears that it’s receiving the incoming request (SYN), and responds appropriately (SYN, ACK), but then Router B responds with Destination unreachable (Network unreachable), which is then, of course, followed by many requests for retransmission as the packets are being dropped. But what’s causing the packets to be dropped? Why aren’t they making it through the network?
EDIT (2024-01-25T08:37Z):
I’m not 100% sure what the previous problem was, but I think that it had to do with the bridge that I was using – not necessarily that it was broken, but perhaps it was jsut incompatible with the setup in some way. What I ended up doing was buying a different router that supported WDS, and then I created a WDS bridge between the two routers. The network seems to be working reliably, and as expected now.

Hmm, I see, it’s not a real L2 bridge, it’s a hacky pretend one that relays.
I don’t have a solution for this particular situation, but I do have a suggestion on how I would do it:
Now, both routers should be able to exchange traffic while being responsible of their own subnet. The only thing missing would be to handle broadcasts so stuff like Bonjour/Avahi works correctly. But as a whole both layer 2 and 3 would behave a bit more cleanly with less surprises.
I think what’s going on is B sorta pretends to be A in some way to do the relaying but something is going wrong.
Alright, I’ll give your suggestion a go.
Done.
Done.
I think I set this right: Network->Routing->Add->(Interface: wwan, Route type: unicast, Target: 192.168.0.1/24, Gateway: 192.168.1.1)
How would I go about doing this? I can’t find any definitive information on how to disable NAT in OpenWRT.
I do need this. I believe this would then require an mDNS reflector, right (it wasn’t required before as relayd was bridging the networks)?
Sounds about right.
That doesn’t seem right. If you’re using the exact same subnet numbers I’ve used for example: that’s be target 192.168.1.0/24 (B’s network) gateway 192.168.0.2 (B’s IP on A’s network as a WiFi client).
Router B is on two networks at the same time: its own (192.168.1.1/24) and A’s network (192.168.0.2/24).
Router A is only on its own network (192.168.0.1/24) and talks to router B as just a client on its network (192.168.0.2). Whenever it has data to send to the 192.168.1.x network, it sends it to 192.168.0.2 which is on that network and will relay it.
Router B would wan configured as a WiFi client with a static IP of 192.168.0.2/24 and default gateway of 192.168.0.1 (router A). The regular default route will do just fine, as that will cover A’s network as well. We’d only need to configure more if there was a third router involved. From there you just need to disable IP masquerading option in Network -> Firewall (you want it unchecked):
You don’t need masquerade even though it’s technically a “wan” because A knows how to send traffic to B’s clients, so B itself doesn’t have to pretend its clients come from itself.
Correct. I found this: https://blog.christophersmart.com/2020/03/30/resolving-mdns-across-vlans-with-avahi-on-openwrt/
If that proves too complicated, I’d consider trying out the GRE tunnel method your original article suggests as an alternative to relayd. It’s kind of like a super basic VPN that I think can be hardware offloaded so I wouldn’t expect much of a performance hit, maybe even less than the relayd option.
Ok, so, I’m ending up with an issue where I can ping Router A from a device on Router B, but I get
Destination Port Unreachableif I try to ping a device on Router A. Likewise, I can ping Router B from a device on Router A, but I getDestination Port Unreachableif I try to ping a device on Router B.I have the route added to Router A (
192.168.1.0/24via192.168.0.2), I have masquerading turned off forwanon Router B.I think you also need to enable full forwarding to and from wan on Router B. I forgot it defaults to not doing that. Set input, output and forward to ACCEPT on Router B on the wan zone, and make sure you also allow forwarding to and from the lan zone. Router A should be fine, I assume A’s WiFi and LAN is the same?
Basically now, Router A sends the traffic to B but B doesn’t forward it to its LAN. But since we don’t have NAT, A’s devices addresses B’s devices directly, not B itself, and there isn’t any connection tracking happening, so it doesn’t “remember” to allow the ping response back in. If you WireShark this, I bet B is successfully sending packets to A and A’s devices, and A’s packets make it all the way to B but B doesn’t forward it to its own LAN, and it stops there.
Can you post the output of
ip roandip aon both routers? (Feel free to redact your public IP/ISP stuff if it shows up)Yep that’s exactly what I see.
I would only be able to for one router. Router A is a tp-link AX73 which doesn’t support OpenWRT. Router B, however, is a tp-link Archer C7 and is flashed with OpenWRT.
Hrm, I still have the same issue. Here’s the firewall settings:
lan zone:
wan zone:
EDIT: I didn’t see your edit, as I hadn’t refreshed the page.
Interesting, lan zone doesn’t allow forward from wan but wan does allow both ways, maybe that’s the one missing. I expect OpenWRT to wire it up both ways automatically… OpenWRT is a mystery sometimes.Actually no, both show unspecified. You need both zones to allow both ways from the other zone.
Alright, I now am able to ping a device on Router B from a device on Router A, but I’m still not able to ping a device on Router A from a device on Router B.
Here’s the firewall settings for Router B:
lan zone:
wan zone:
EDIT:
Scratch that! apparently it is working. I could’ve sworn that I checked the ping. Maybe I subconciously applied something else.
I’m now encountering another issue where I can’t ping any external IP’s. I don’t mean that DNS isn’t resolving (I set that on Router B to use Router A as the DNS resolver), but the I can’t ping, say,
google.com, for example, from a device on Router B. I can see the ICMP requests in Wireshark, but they just say “no response”.Erm, okay that’s not looking promising. It’s starting to look like Router A doesn’t like this setup at all. It’s not routing B’s traffic, possibly because it’s not the subnet it expects to serve. Ugh. Check all the options you can in Router A if you can find something that will allow it to work.
You can fairly easily test that by enabling masquerading on B. It’ll break most of what we just set up but it’ll confirm that.
We still have some options on the OpenWRT side to make it masquerade only public traffic but now I’m wondering if A will even let you port forward to something on B. I would try that now and see if it works.
Is A able to ping B and devices on B, or only on A? A itself has a route for B’s subnet right?