Until yesterday, I didn’t even know you could use the docker images and the same docker-compose configs with Podman.
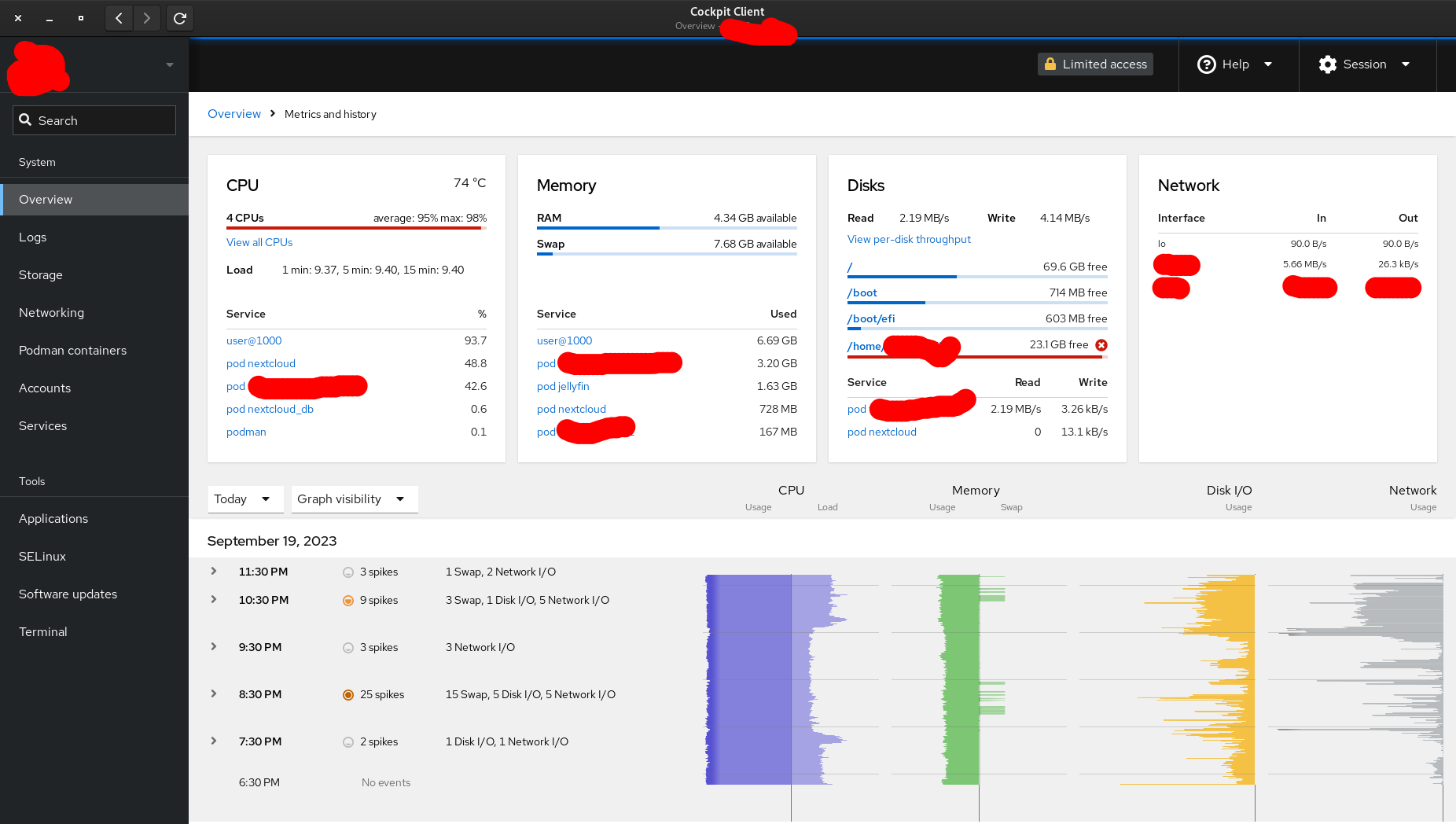
The UI you are looking at is Cockpit, which can be installed on almost any Linux Server. I have used it before but I am amazed by its integration with Podman.
Seriously, consider trying this, once.
Here’s another screenshot of Cockpit:


I originally excited by Podman, but ultimately migrated away from it. Friendship ended with Ubuntu and Docker -> CentOS and Podman -> Proxmox + Debian LXC (which has its own irritations but anyway). Off the top of my head:
I brought all this up in another community and was told the problem was [paraphrased] “people keep trying to use Podman like they use Docker” - whatever that means. I do like a number of design choices in it, like including the command used to create containers in the metadata, and how it’s easy to integrate into SystemD for things like scheduled updates.
Cockpit is pretty slick though, need to install it on my bare metal Debian host.
how do you use proxmox + debian lxc?
I use that too, but run services + caddy reverse proxy with docker compose inside
I’ve read that docker should not be used inside containers, but it has worked for me. I have wireguard in a VM, I think I had some issues there
Mostly just as a wrapper for Docker. The main issue I’ve run into is Docker’s union file system functionality doesn’t work when backed by ZFS, so disk usage can balloon out of control. I wouldn’t use this in production but don’t tell me how to live my life mom.
Beyond various Docker stacks I also have a Certbot container that uses Snap (sigh), and Hashicorp Vault container which runs as a vanilla SystemD service. I run Wireguard as part of my OPNSense VM. That’s something I would run in a VM since it’s exposed to the internet. I have an older MinIO and Concourse CI Docker Compose config that I’d love to run in LXC but I suspect that isn’t realistic.
Note on Vault, I haven’t been able to get mlock to work (used to prevent sensitive memory from being swapped). By all accounts it should just work in LXC, but since it isn’t and there’s no swap on the host I just turned it off. I may migrate Vault to a VM at some point.
I’m personally just interested in lightweight environments with good enough isolation and don’t break all the time over nothing. Docker mostly accomplishes that for me. LXC + Docker also mostly accomplishes that.
(My heart yearns for FreeBSD Jails but with decent tooling)
I use Docker inside Debian LXC on Proxmox, there’s a way to avoid the crazy disk usage and it works really nicely. I followed these blog posts:
https://theorangeone.net/posts/docker-in-lxc/
https://theorangeone.net/posts/docker-lxc-storage/
I’m certainly not using it in production but it’s great in the home lab.