- 12 Posts
- 17 Comments

 1·2 months ago
1·2 months agoThanks for the links, but 10minutemail.org is loaded with crap.

 3·2 months ago
3·2 months agoWell received, any sources where we could corroborate that statement ?

 1·2 months ago
1·2 months agoDamn
now that I open few ports
9001I see incoming connection that are dropped because they use totally diffrent ports
drop: IN=eth0 OUT= MAC=aMacadrs SRC=aIP DST=aMyIP LEN=64 TOS=0x00 PREC=0x00 TTL=48 ID=65508 DF PROTO=TCP SPT=443 DPT=50194 WINDOW=501 RES=0x00 ACK URGP=0privacy
I’ve replaced some string with
'aSomething'.
it’s weird in my nftable config file I have
type filter hook input priority 0; policy drop; ct state established,related acceptAny ideas ?

 4·2 months ago
4·2 months agoThank you ! @thingsiplay@beehaw.org 👍
-Esolved it :)

 1·2 months ago
1·2 months agoYes

 2·2 months ago
2·2 months ago👍 Thanks again @qprimed@lemmy.ml

 2·2 months ago
2·2 months agoThank you very much @qprimed@lemmy.ml ! indeed I saw in my nftables log tentative to 443 and 9001. ( I didn’t find this in the
tordoc … )9050 is your socks proxy - so protect it. if your nftables is blocking localhost:9050/TCP then you need to correct that.
is this will do :
ip saddr 127.0.0.1 ip daddr 127.0.0.1 accept?
I couldn’t have said it better !

 1·9 months ago
1·9 months agoI’ve did some more digging.
and Briar still remain better at security level !
The big downside of SimpleX is that it’s not P2P and IP correlation by watching your traffic is possible.
SimpleX recommend to use Tor on top of it with for example Orbot. That’s a good idea, but not the best to convince none-tech folks to adopt it. (it’s already so hard to change peoples habit… ) Tor should be embedded.
As soon Tor is embedded I will migrate to it. SimpleX have nice thought features and it’s easy to use.

 2·9 months ago
2·9 months agoThey did the same with Flash with the help of adobe.

 1·9 months ago
1·9 months agoThank you very much @jet@hackertalks.com & @Quexotic@beehaw.org
The EFF article is really interesting for everyone. ( I was aware of this )
Indeed no one should assume that his packets are not intercepted along the road. But conceive an software that on top of that, specifically route the traffic trough his server not make it better (on the opposite in my opinion)
Even if the owner of those server do not process the data… ( This is relying on blind trust) those servers might be breached. (in addition to the systemic data recording, like in the EFF article )
Let put it simple, is SimpleX offer on the actual Internet (can’t wait the next gen, GNUnet or anything similar) a similar level of Trust & privacy than Briar ?

 1·9 months ago
1·9 months agoA little update.
I’ve just tested simplex on Android.
it’s very well thought out ! The features make sense. UNFORTUNATELY it’s not P2P ! all the messages pass by their servers :'( with Briar it’s P2P… weirdly they claim their way is better than P2P ! any comment on that ?
In my point of view, if messages are stored somewhere it’s mean the can be process[1] !
Cheers.
edit: lemmy link to their community !simplex@lemmy.ml
Copied, analyzed, cracked (Brut force or what ever) ↩︎

 1·9 months ago
1·9 months agojami’s good but it uses turn server to verify your name
So is it secure ? does that mean you rely on those server to be able to created an account ?

 1·9 months ago
1·9 months agoThough android only.
Anyway on Windows, Apple there is no sense to have a privacy apps if the OS it self pump everything it can.
And on Android it only make sense if you use an AOSP rom, or another but without the google crapware…

 2·9 months ago
2·9 months agoI think your mistaken… Can someone confirm ?
So I was eager to test Jami, but on Windows it require Windows 10… so no way --> https://itvision.altervista.org/why-windows-10-sucks.html
anyway I gave a quick try on a test machine (win10) But I got , not matter what I entered
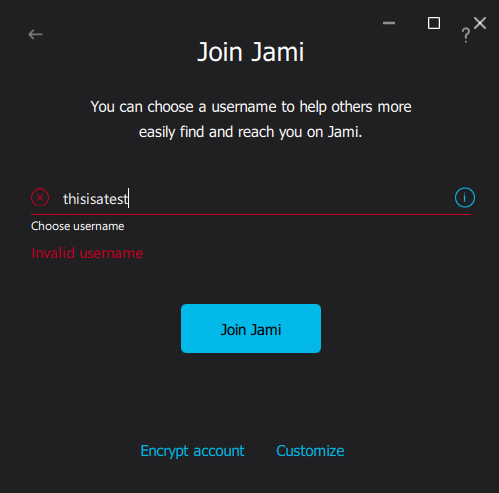
Too bad because it had on paper, a lot of nice features…
On linux, too bad they don’t provide (yet) an AppImage…

 0·11 months ago
0·11 months agono ! thanks ! look promising too.
I’ll try it and give my review… but is it require to make a “jami” account on their server !??


Thank you @Anafabula@discuss.tchncs.de ! it works !
I’m wondering whats is the option: (9) ECC and ECC ?? I found nothing in their documentation :/